10 Types of Crypto Scams and How They Operate
Crypto has opened up new ways to invest, send money, and even earn income online. But alongside the opportunities, scams have grown just as quickly. If you’re involved in crypto at any level, knowing how these scams work isn’t optional, it’s necessary.
This isn’t about fear. It’s about awareness. Once you understand the patterns, most scams become easier to spot, and easier to avoid.
- 10 Types of Crypto Scams and How They Operate
- Practical Tip
- 2. Ponzi and Pyramid Schemes
- 3. Fake Crypto Exchanges
- 4. Rug Pulls
- 5. Pump and Dump Schemes
- 6. Giveaway Scams
- 7. Romance Scams Involving Crypto
- 8. Malware and Crypto Wallet Hacks
- 9. Fake Investment Opportunities
- 10. Impersonation Scams
- Patterns Most Crypto Scams Share
- How to Protect Yourself
Why Crypto Scams Are So Common
Before getting into the types, it helps to understand why crypto is a target.
- Transactions are irreversible
- Many users are still learning how crypto works
- Scammers can stay anonymous
- There’s less regulation compared to traditional finance
Another key issue is the gap between holding crypto and actually using it safely in everyday transactions. When users rely on unfamiliar platforms or shortcuts, they become easier targets. This is where structured solutions, like platforms that let you spend crypto securely without exposing your wallet, can reduce risk.
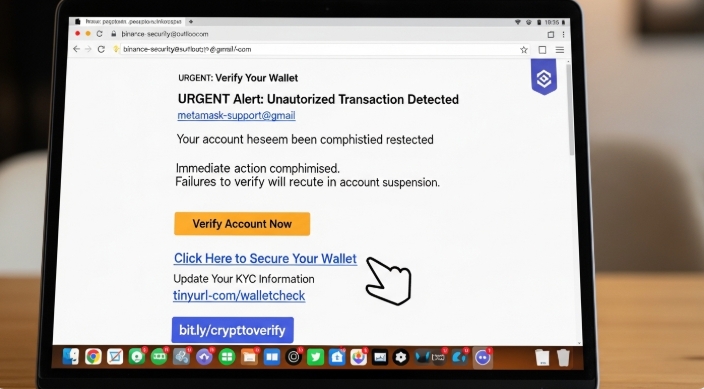
1. Phishing Scams
How It Works
Phishing scams trick you into giving away sensitive information like your wallet password or private keys. This usually happens through fake emails, websites, or messages that look legitimate.
What It Looks Like
- Emails pretending to be from exchanges
- Fake login pages that mirror real platforms
- Messages urging you to “secure your account”
Practical Tip
Always double-check URLs before logging in. If a platform sends you a link, don’t click it, go directly to the official site instead.
If you regularly make payments or subscriptions with crypto, using a layer like Bycard helps reduce how often you need to connect your wallet directly, limiting exposure to phishing attempts.
2. Ponzi and Pyramid Schemes
How It Works
These scams promise high returns with little or no risk. Early investors are paid using money from new investors, not actual profits.
What It Looks Like
- “Guaranteed returns”
- Referral-based earnings
- Pressure to recruit others
Practical Tip
If returns sound unrealistic or depend heavily on bringing in new people, it’s a red flag.
3. Fake Crypto Exchanges
How It Works
Scammers create fake trading platforms that look real. You deposit funds, but once you try to withdraw, you’re blocked.
What It Looks Like
- Attractive bonuses for signing up
- Poor or no withdrawal functionality
- Little to no online reputation
Practical Tip
Stick to well-known exchanges and always check reviews before signing up.
Also, avoid leaving funds sitting on unfamiliar platforms. Moving your crypto into tools that are built for controlled spending, like Bycard, can reduce how much you expose to unknown exchanges.
4. Rug Pulls
How It Works
Developers launch a new crypto project, hype it up, attract investors, and then suddenly withdraw all the funds.
What It Looks Like
- New tokens with aggressive marketing
- Anonymous developers
- Sudden disappearance of liquidity
Practical Tip
Research the team behind any project. If you can’t verify who they are, proceed cautiously.
It also helps to avoid locking all your funds into new projects. Keeping a portion accessible through secure spending solutions ensures you’re not completely tied to risky ecosystems.
5. Pump and Dump Schemes
How It Works
A group artificially inflates the price of a coin through hype, then sells off their holdings, leaving others with losses.
What It Looks Like
- Sudden price spikes with no real news
- Social media hype pushing a “hidden gem”
- Urgency to “buy now”
Practical Tip
Avoid making decisions based on hype. Look for real utility and long-term value.
6. Giveaway Scams
How It Works
Scammers pretend to be influencers or companies offering free crypto. You’re asked to send a small amount to “verify” your wallet, and you never get anything back.
What It Looks Like
- “Send 0.1 BTC, get 1 BTC back
- Fake celebrity endorsements
- Urgent, limited-time offers
Practical Tip
No legitimate giveaway requires you to send money first. That’s always a scam.
Using structured payment tools like Bycard also removes the need to respond to random “opportunities” just to access liquidity, you already have a controlled way to spend your funds.
7. Romance Scams Involving Crypto
How It Works
Scammers build emotional relationships online, then convince victims to invest in fake crypto opportunities.
What It Looks Like
- Sudden financial advice from someone you just met
- Requests to invest on specific platforms
- Emotional pressure tied to money
Practical Tip
Keep finances separate from online relationships, especially if you haven’t met in real life.
Having clear boundaries between your crypto storage and spending methods helps here. You’re less likely to transfer funds impulsively when your assets are managed through structured systems rather than quick wallet transfers.
8. Malware and Crypto Wallet Hacks

How It Works
Malicious software is used to gain access to your wallet or track your keystrokes.
What It Looks Like
- Fake apps or browser extensions
- Downloads from unofficial sources
- Unexpected system behavior
Practical Tip
Only download apps from official stores and use hardware wallets when possible.
Another layer of protection is limiting how often your wallet is directly exposed. By using services like Bycard for transactions, you reduce repeated wallet interactions, which lowers your attack surface.

Perfect Card for running ads!

9. Fake Investment Opportunities
How It Works
Scammers present “investment managers” or “trading bots” that promise consistent profits.
What It Looks Like
- Professional-looking dashboards
- Daily or weekly profit guarantees
- Requests to hand over funds for management
Practical Tip
If someone is offering to manage your crypto for guaranteed returns, walk away.
10. Impersonation Scams
How It Works
Scammers pose as customer support agents, influencers, or even friends to gain your trust and access your funds.
What It Looks Like
- Fake social media accounts
- Direct messages offering help
- Requests for private keys or login details
Practical Tip
No legitimate support team will ever ask for your private keys or passwords. If you ever need support, go through official channels only. Avoid responding to unsolicited messages, especially when they involve your wallet or transactions.
Patterns Most Crypto Scams Share

Even though the tactics differ, most scams follow similar patterns:
- Urgency: “Act now or miss out.”
- Emotional pressure: Fear or excitement
- Too-good-to-be-true returns
- Lack of transparency
Once you recognize these patterns, it becomes easier to pause and think before acting.
How to Protect Yourself
Crypto can feel exciting, but it’s also a space where mistakes can be costly. Protecting yourself doesn’t have to be complicated; it’s mostly about habits and using the right tools. Here’s how:
- Use two-factor authentication on all accounts
Adding 2FA (like an app or SMS code) makes it much harder for hackers to access your accounts, even if they get your password. It’s a simple step that blocks most unauthorized access attempts. - Store assets in secure wallets (preferably hardware wallets)
Don’t keep all your crypto on exchanges. Hardware wallets store your private keys offline, reducing the risk of hacks or malware. Treat them like your digital vault. - Verify links before clicking
Scammers often use fake emails or social media links to trick you. Always double-check URLs by typing them manually into your browser, and never click suspicious links—even if they look urgent. - Avoid sharing private keys, ever
Your private key is the only way to access your crypto. No one should ever ask for it, legitimate platforms and support teams don’t need it. Sharing it is basically giving your crypto away. - Research every platform before investing
Before using any exchange, investment platform, or new token, check reviews, verify the team behind it, and look for any red flags. If information is missing or the project seems rushed, it’s safer to skip it. - Use structured tools (like Bycard) to separate spending from storage
Bycard allows you to use crypto for payments without constantly exposing your main wallet. Separating storage from spending minimizes risk and prevents accidental losses in scams or hacks. - Be skeptical of unsolicited messages
Whether it’s social media DMs, emails, or texts, if someone contacts you unexpectedly about crypto, be cautious. Scammers often pose as support agents, influencers, or even friends to gain access to your funds.
Conclusion
Crypto scams aren’t always obvious at first glance. Many of them look polished, convincing, and even professional. But when you slow down and examine the details, the warning signs usually show up.
The goal isn’t to avoid crypto, it’s to approach it with awareness. And more importantly, to use systems that reduce unnecessary risk.
Because in crypto, how you use your assets matters just as much as where you store them.